 How To Set Up Internet Or APN Settings On Huawei Phones How To Set Up Internet Or APN Settings On Huawei Phones
Today we are going to learn how to setup internet settings or APN on Huawei Mobile Phones. The internet connection is shared by many functions on your phone such as internet browsing, receiving email messages and installing apps. You can access the internet as soon as you've inserted your SIM in your Huawei mobile phones. If this isn't the case, you can set up your phone for internet manually by following the steps below.
Step 1. Find Access Point Names . Press Settings icon Step 2. Now Press Mobile Network. Step 3. Press Mobile Data. Step 4. Press Access Point Names (AP Ns) below the required SIM. Step 5. Press the Menu Icon. Step 6. Its time to create new data connections: Press New APN. Step 7. Press Name. Step 8. Under the "Name" field, and enter in your mobile Services Providers name. for example, Vodafone. Step 9 . Press APN.
0 Comments
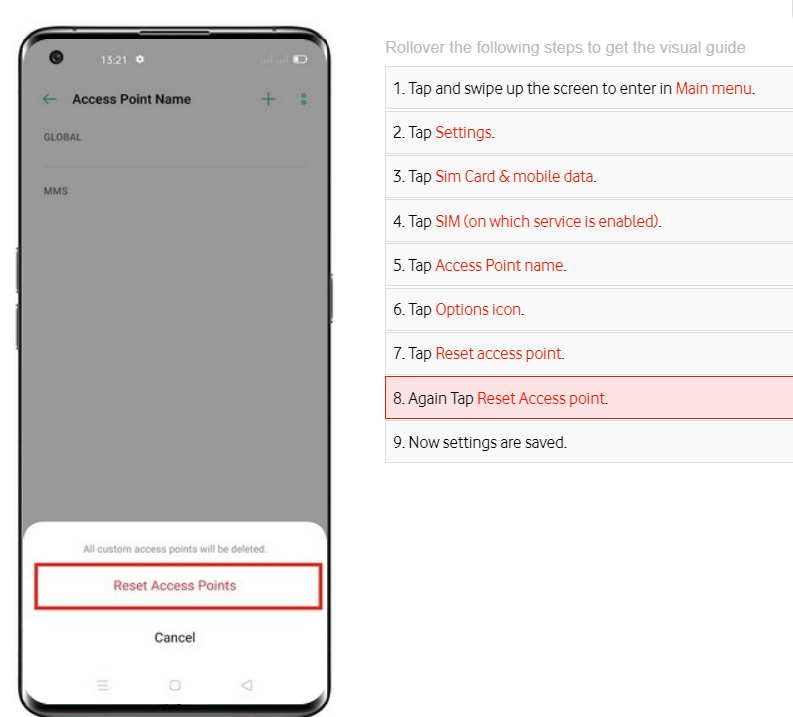
Today we are going to learn how to setup internet settings or APN on OPPO find x3 lite, The internet connection is shared by many functions on your phone such as internet browsing, receiving email messages and installing apps. You can access the internet as soon as you've inserted your SIM in your Oppo find X3 lite mobile phone. If this isn't the case, you can set up your phone for internet manually by following the steps below.

Today we are going to learn how to setup internet settings or APN on OPPO phones like Oppo Find N2 Flip, Oppo a78 5G, Oppo A57s , Oppo Find 5x Lite, Oppo Find x5 Pro 5G, Oppo Find x3 pro,Oppo find x3 lite, The internet connection is shared by many functions on your phone such as internet browsing, receiving email messages and installing apps. You can access the internet as soon as you've inserted your SIM. If this isn't the case, you can set up your phone for internet manually.
 How To Avoid Ransomware Virus Or Malware How To Avoid Ransomware Virus Or Malware Ransomware is a form of malware that provides criminals with the ability to lock a computer from a remote location – then display a pop-up window informing the owner or user that it will not be unlocked until a sum of money is paid. Recent well-publicised examples are CryptoLocker, Cryptowall and WannaCry (and variants of these under different names). In some cases, the only usable part of the computer is the number keypad to enter a PIN to enable payment to the criminals. An additional twist is that an accusation of illegal activity or a pornographic image may sometimes appear on the locked screen, making it more difficult through embarrassment for some users to seek help from anybody else, and simply resort to paying the ransom. 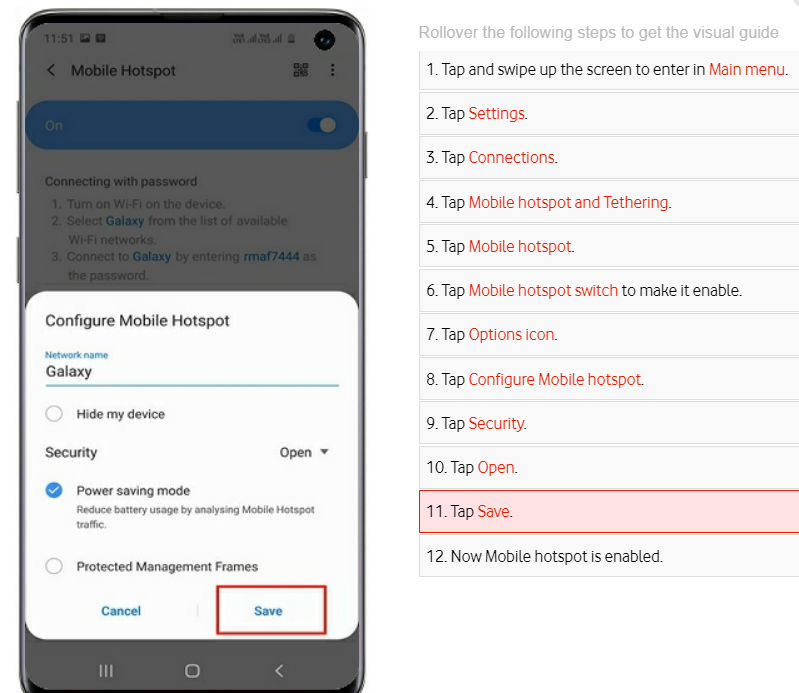 Rollover the following steps to get the visual guide on how to enable WiFi hotspot on Samsung Galaxy S10 brand.
 You can follow the steps below to reset your Oppo Find X2 phone to its default settings. Warning! You are to back up for data (photos and other files before your do the default settings reset.
 To the average Papua New Guineans, figuring out how to save money while raising a family is no small feat. The average cost of raising a child born in today’s world until ready to be independent is quite a fortune. Whether you’ve got one child or a growing brood, it pays to consider ways to save money on family expenses. Check out these money-saving tips for families:
Forget sequences from blockbuster films of gangs breaking into secure buildings, avoiding guards to attach a “tap” to a blinking server. Real hackers walk through the front door by sending you an email. “Ninety per cent of cyber attacks worldwide begin with an email. Most organisations don’t really look at their email security that carefully,” said Michael Connory, chief executive of Security In Depth. “Everybody is vulnerable. Australian organisations have no idea how vulnerable they are.” After a cyber breach of the Federal Parliament’s computer network and a warning from one of Australia’s most senior military figures that the threat of similar attacks is on the rise, experts are pleading with Australian businesses to take the threat seriously. “The easiest way for an attacker to get into an organisation is by phishing, by email,” Mr Connory explained. It’s simple. Somebody in an organisation opens an email and are directed to click on a link, usually something that requires an action such as: “You need to update your details”. When the person logs in, they inadvertently give their username and password to a hacker. The information is then used to get into the broader computer systems of an organisation. |
Tech Tips, Computers Resources,Get all your computer tech information, textbook, and games for free here. Also visit out latest Technology site : Categories
All
|
- Home
- News
- Business News
- Economy News
- Sports News
- International News
- Corruption News
- Mining Watch
- Jobs
- Education News
- Scholarships
- Health News
- Bzzmart Online Shopping Platform
- Pacific
- Used Cars
- Buy or Rent Homes
-
Travel
- City of Port Moresby
- Adventure and Destination
- Hotels & Lodges in PNG
- Hotels & Lodges in Mendi, Southern Highlands Province
- Hotels & Lodges in Lorengau, Manus Province
- Hotels in Oro Province
- Hotels and Lodges in ESP
- Hotels & Lodges in Kavieng
- Hotels and lodges in Kimbe
- PNG Photo Gallery
- Map of Papua New Guinea
- PNG
-
Computer Tech
- Tech Help
-
Top Weebly designed Websites
>
- HOW TO RECOVER FILES WITH SHORT CUTS OR HIDDEN IN FLASH DRIVE OR EXTERNAL HARD DRIVE
- How to remove Stubborn Computer Virus
- Creating Login or Sign in Membership page in Weebly sites
- How to auto insert Table of Content in Word
- Top Weebly Website Examples and Portfolio
- Weebly Membership Sign in feature available
- Send Free SMS in PNG
- Radio Stations
- Television stations >
- PNG Information Directory
- Computer Resources
- Classifieds
- About us
- Contact Us
- Competition
- Advertisement
- Privacy Policy
- SP PNG Hunters News
- Weebly Forums
- National Football Stadium, Port Moresby
- Work Permits and VISAs in PNG : Guide
- Seasonal Workers Program for PNG
- List Your Business on PNGFacts.com
- Twodot Business Solutions
- Become a Sponsor
- Mt Giluwe Lodge
- Papua New Guinea Defence Force
- Political parties in PNG
- NID PNG
- Employment VISA in PNG
- Business VISA
- Visitor VISA
- Police Clearance in Solomon Islands
- PNG Electoral Commission
- PNG Election Results
|
Search Papua New Guinea Database >>
|
|
|
|
|
Home: PNG News :Travel : Government System: Computer Tech : About us: Contact : Disclaimer : Sitemap : Login Copyright & Disclaimer © 2012 -2023 PNG Facts: All rights reserved:
|
Website developed by Kilikalo Technology & Business Solutions Ltd
About |
Terms |
|
 RSS Feed
RSS Feed